A cyber range is a controlled, realistic environment where individuals and teams practice cybersecurity skills against simulated threats. Think of it as a flight simulator for cybersecurity professionals: a place where you can experience realistic attack scenarios, make mistakes, and learn from them -- without putting production systems at risk.
The concept emerged from military training environments in the early 2000s, where defence organizations needed realistic cyber warfare training grounds. Today, cyber ranges have evolved far beyond their military origins and are used by enterprises, government agencies, academic institutions, and critical infrastructure operators worldwide.
In an era where the global cybersecurity workforce shortage exceeds 3.4 million professionals (ISC2, 2024), and the average cost of a data breach continues to rise, cyber ranges have become essential infrastructure for any organization serious about building and maintaining cyber readiness.
Types of Cyber Ranges
Not all cyber ranges are created equal. The three primary deployment models each come with distinct trade-offs in realism, cost, scalability, and security.
Dedicated Hardware
Physical servers and networking equipment in a dedicated facility. Maximum realism and isolation, but highest cost and limited scalability. Common in military and national security contexts.
Cloud-Based
Virtual infrastructure provisioned on-demand from cloud providers. Excellent scalability and lower upfront cost, but dependent on internet connectivity and external cloud services.
Hybrid / On-Premises
Private cloud infrastructure (such as OpenStack) deployed on-premises with optional air-gap capability. Balances realism, control, and scalability. Increasingly the preferred model.
The hybrid model has gained significant traction because it allows organizations to maintain complete data sovereignty while benefiting from the flexibility of virtualized infrastructure. An air-gapped on-premises deployment means that no training data, exercise content, or participant information ever leaves the organization's physical boundary -- a requirement for many defence and government customers.
Key Capabilities of a Modern Cyber Range
A world-class cyber range goes far beyond spinning up a few virtual machines. Here are the capabilities that distinguish production-grade platforms from basic lab environments.
Multiple Exercise Families
Support for diverse training modalities: CTF Challenges for individual skill challenges, Battle Stations (CDX) for team-based defence, Wargames (ADX) for red vs blue competitions, Training Courses (TLX) for guided learning, and Crisis Simulation for executive decision-making.
Automated Scoring and Assessment
Per-objective automated grading with dynamic flags that are unique to each participant, preventing flag sharing. HMAC-based flag generation, real-time leaderboards, and detailed post-exercise analytics.
Realistic Infrastructure Orchestration
The ability to provision complex, multi-VM environments with realistic services: Active Directory, SIEM, IDS/IPS, firewalls, web servers, databases, and OT/ICS components -- all isolated per exercise instance.
Content Library and Customization
A rich library of pre-built exercises spanning web security, network exploitation, forensics, reverse engineering, OT/ICS, and more. Plus tools for organizations to create and customize their own exercises.
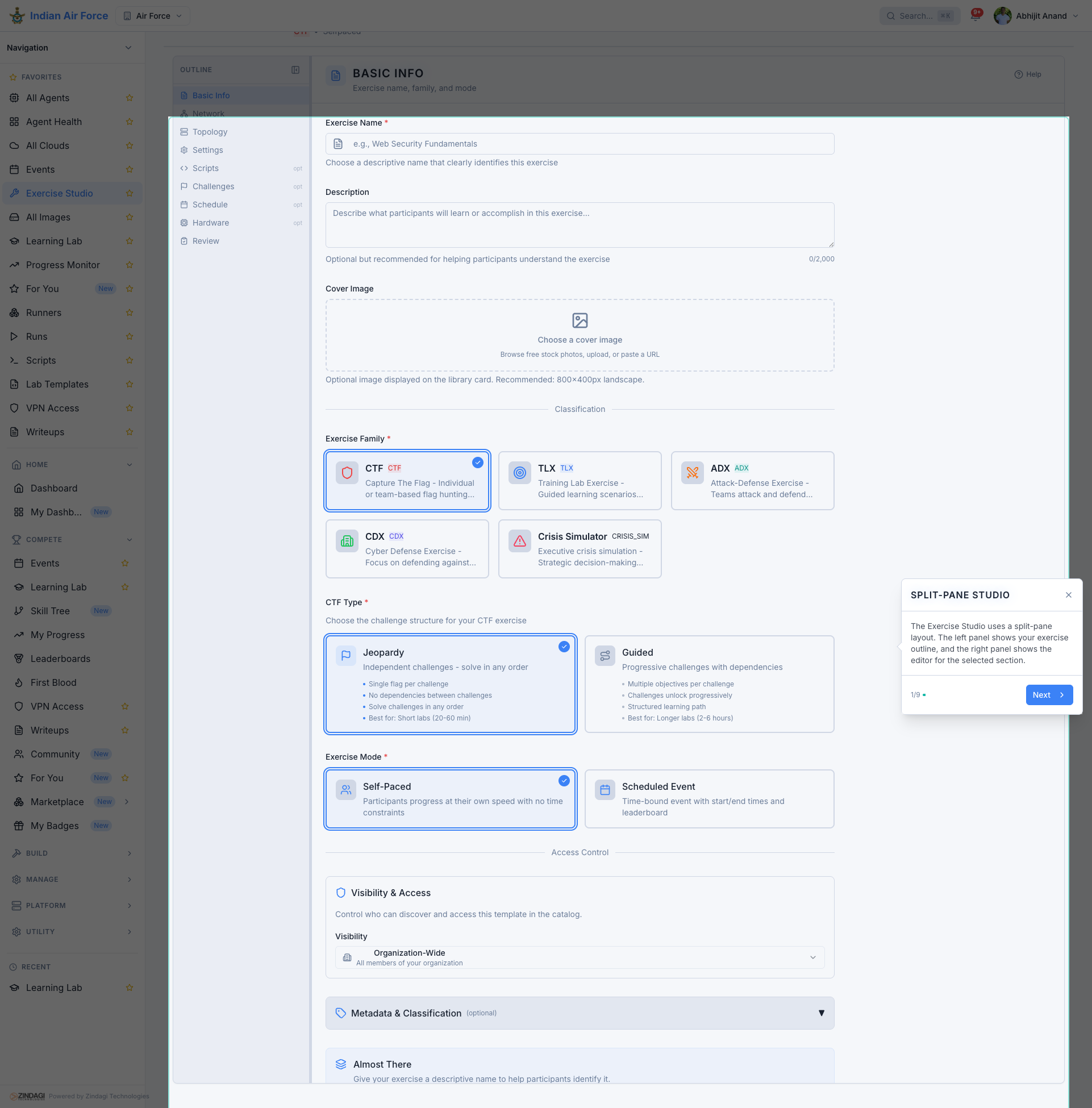
The Exercise Studio: a split-pane exercise builder with outline tree, challenge editor, and visual topology designer.
Who Uses Cyber Ranges?
Cyber ranges serve a diverse set of stakeholders, each with unique requirements and training objectives.
Military and Defence
Armed forces use cyber ranges for joint cyberspace operations training, red team development, and mission rehearsal. Requirements include air-gap deployment, sovereign hosting, and alignment with national cyber doctrine.
Enterprise and SOC Teams
Security operations centers use cyber ranges to train analysts on incident response, threat hunting, and SIEM operations. Enterprises use them for skills gap assessment and compliance readiness.
Academia and Universities
Universities integrate cyber ranges into cybersecurity curricula for hands-on lab assignments, student competitions, and research. Requirements include multi-tenant isolation for different courses and auto-grading for large cohorts.
Critical Infrastructure and OT/ICS
Operators of power grids, water systems, manufacturing plants, and oil and gas facilities use cyber ranges to train on OT-specific threats. Exercises involve SCADA systems, PLCs, industrial protocols (Modbus, DNP3, OPC UA), and digital twins.
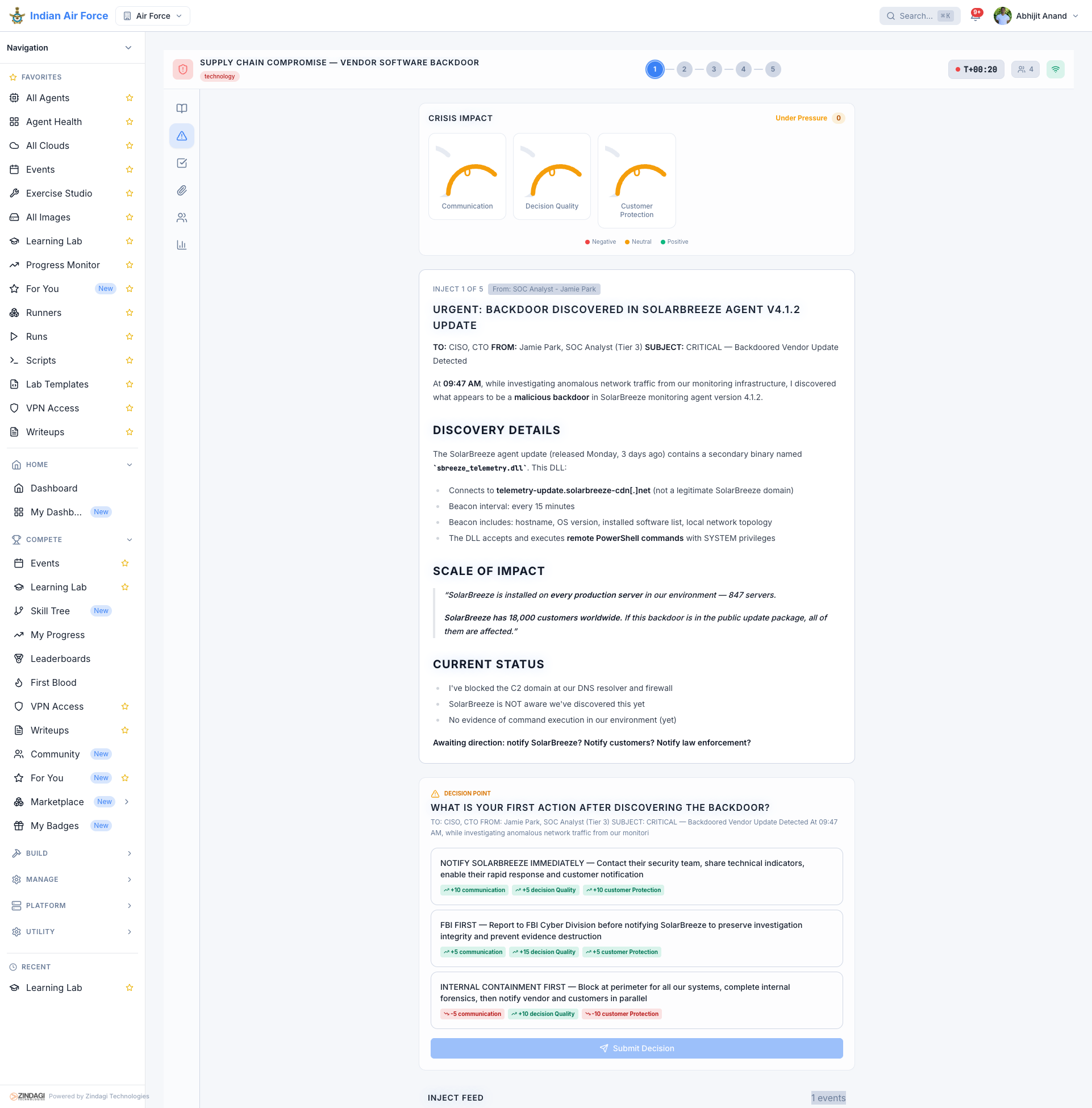
A live crisis simulation exercise with scenario injects, AI NPC stakeholders, and executive decision tracking.
How to Evaluate a Cyber Range: 10 Criteria
Whether you are procuring a cyber range for a defence establishment, a university, or an enterprise SOC, these ten criteria will help you make an informed evaluation.
- 1Exercise diversity: Does it support multiple exercise families (CTF Challenges, Battle Stations, Wargames, Training Courses, crisis simulation)?
- 2Infrastructure realism: Can it deploy full enterprise networks with Active Directory, SIEM, IDS, and OT/ICS systems?
- 3Scalability: How many concurrent participants and parallel exercise instances can it support?
- 4Deployment flexibility: Does it offer on-premises, cloud, hybrid, and air-gapped deployment options?
- 5Multi-tenancy: Can it isolate training environments, data, and administration across multiple teams or organizations?
- 6Scoring and assessment: Does it provide automated scoring with per-participant dynamic flags and objective-level grading?
- 7Content depth: How many exercises are available, and do they cover your target domains (IT, OT, cloud, mobile)?
- 8Customization: Can you create custom exercises, white-label the platform, and tailor the experience to your institution?
- 9Reporting and analytics: Does it provide skills gap analysis, individual progress tracking, and NICE/MITRE framework mapping?
- 10Total cost of ownership: Consider licensing, infrastructure, support, customization, and long-term vendor independence.
Pro tip: Ask each vendor for a live demonstration with a realistic exercise scenario -- not just a slide deck. The best way to evaluate a cyber range is to experience it as a participant. Pay attention to provisioning speed, exercise realism, scoring accuracy, and the overall user experience.
The Future of Cyber Ranges
The cyber range industry is evolving rapidly, driven by several key trends that will shape the next generation of platforms.
AI-Powered Adaptive Training
Artificial intelligence is transforming cyber ranges from static exercise environments into adaptive training systems. AI-powered difficulty calibration, intelligent hint systems, automated adversary simulation, and personalized learning paths will become standard features. Expect AI NPCs in crisis simulations that respond dynamically to participant decisions.
OT/ICS and Multi-Domain Convergence
As IT and OT environments converge, cyber ranges must support training across both domains simultaneously. Future platforms will integrate IT infrastructure, OT/ICS systems, cloud environments, mobile devices, and even RF/EW (radio frequency / electronic warfare) capabilities into unified exercise scenarios.
Sovereign and Air-Gapped Deployment
With increasing emphasis on data sovereignty and digital autonomy, more nations are requiring cyber range platforms that can be deployed entirely on sovereign infrastructure with no external dependencies. This trend will accelerate the development of fully self-contained, air-gappable platforms that operate without external cloud services or telemetry.
Conclusion
A cyber range is no longer a nice-to-have for cybersecurity training -- it is essential infrastructure. Whether you are training military cyber warriors, developing SOC analysts, educating the next generation of security professionals, or building resilience in critical infrastructure operators, a well-designed cyber range provides the realistic, hands-on experience that no textbook, certification course, or tabletop exercise can match.
The key is choosing a platform that matches your specific requirements: exercise diversity, deployment flexibility, scalability, content depth, and total cost of ownership. Use the 10-point evaluation framework above to guide your procurement process, and always insist on a live demonstration before making a decision.
The organizations that invest in cyber range training today will be the ones best prepared to defend against the threats of tomorrow.