Network Resilience for Indian Telecom
BSNL breached twice in 12 months. 278GB of subscriber data stolen. 5G expands the attack surface. Build resilience with telecom-specific cyber training.
The Telecom Threat Landscape
India's telecom networks carry a billion subscribers and a nation's communications. The breaches are real, the mandates are here, and the attack surface is growing.
BSNL Breached Twice in 12 Months
278GB StolenBSNL suffered two major breaches in 2024 — 278GB of subscriber data stolen including IMSI numbers, SIM details, and server snapshots. Attackers sold access for $5,000.
5G Expands the Attack Surface
India's 5G rollout introduces network slicing, MEC edge computing, and NFV/SDN — each a new attack vector. Security teams need to train on 5G-native threats, not retrofitted 4G scenarios.
DoT & TCS Rules 2024
The Telecommunications Security Directive and Telecom Cyber Security (TCS) Rules 2024 mandate security audits, incident reporting, and subscriber data protection for all TSPs.
Nation-State Targeting
Telecom networks are strategic targets for nation-state actors seeking surveillance access, traffic interception, and subscriber data for intelligence collection.
Telecom-Specific Training Scenarios
From SS7 signaling attacks to 5G core compromise — exercises built on real telecom TTPs, not generic network scenarios with telecom labels.
5G Core Network Slicing
Attacks targeting network slice isolation, slice-level DoS, and cross-slice data leakage. Operators learn to detect and contain breaches within specific network slices.
SS7/Diameter Exploitation
Signaling protocol attacks including location tracking, call interception, SMS interception, and authentication bypass via SS7 and Diameter vulnerabilities.
BGP Hijack & Route Leak
Border Gateway Protocol hijacking, route leak detection, and prefix filtering exercises. Realistic multi-AS topology with RPKI validation training.
SIM Swap & IMSI Cloning
SIM swap fraud detection, IMSI catcher identification, and subscriber authentication bypass scenarios modeled on real Indian telecom fraud cases.
Subscriber DB Exfiltration
Exercises covering HSS/UDM compromise, CDR theft, and subscriber data exfiltration — modeled on the BSNL breach TTPs with detection and containment training.
NFV Core Compromise
Attacks on virtualized network functions, MANO orchestrator exploitation, and container escape scenarios targeting the 5G core infrastructure.
Platform in Action
Real product screenshots from telecom security training environments.
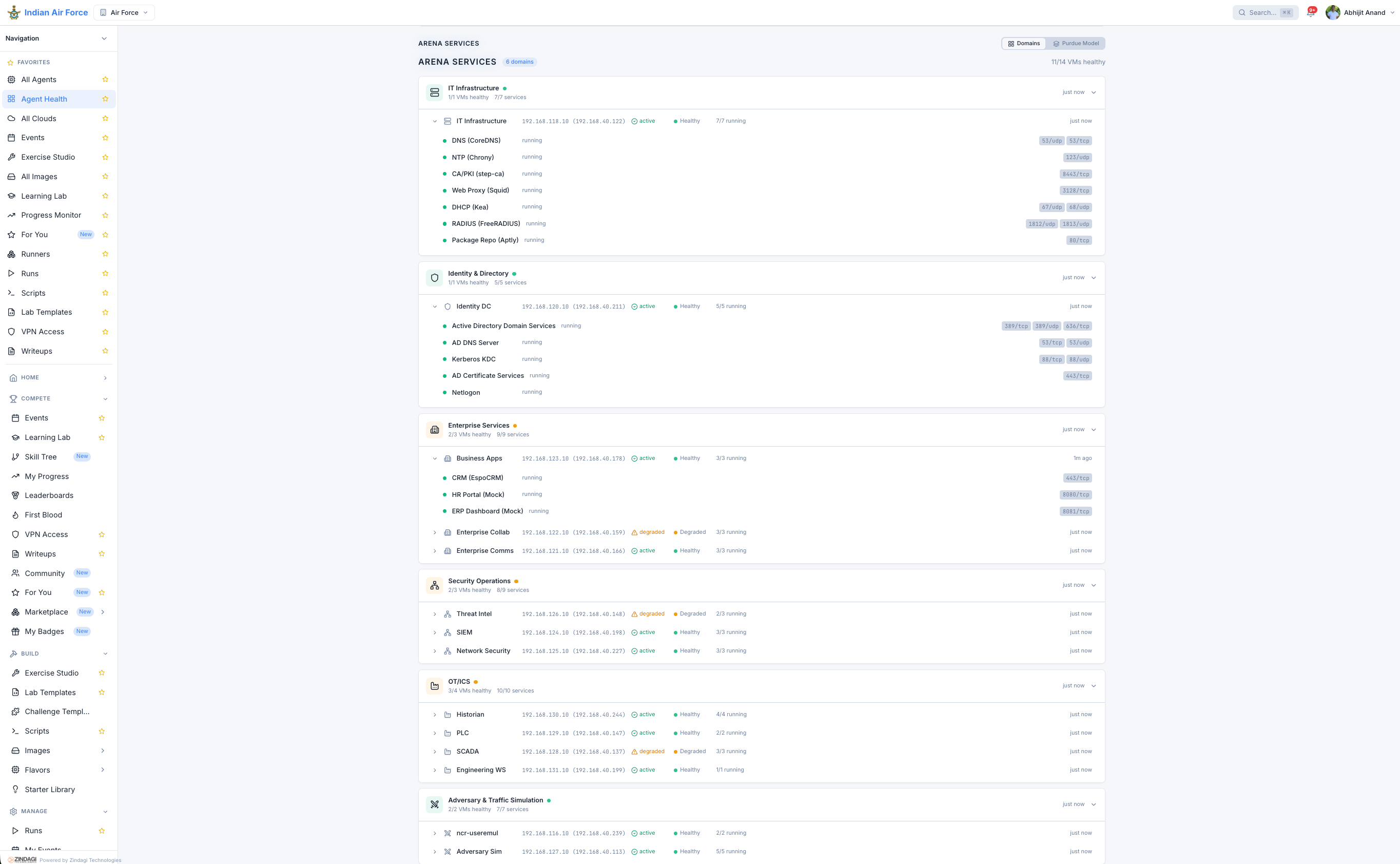
Multi-service arena deployment with network function simulation and attack surface mapping.
Advanced & Emerging Threats
Stay ahead of the threat curve with exercises covering MEC edge attacks, telecom fraud, and Zero Trust validation.
MEC Edge Attacks
Multi-access Edge Computing exploitation including edge application compromise, data plane interception, and lateral movement from edge to core.
Telecom Fraud (IRSF/Wangiri)
International Revenue Share Fraud and Wangiri callback fraud detection. Operators learn real-time fraud pattern recognition and automated blocking.
DNS Poisoning & Hijack
Telecom DNS infrastructure attacks targeting subscriber resolution, CDN steering manipulation, and lawful intercept system compromise.
Zero Trust Network Access
Validate Zero Trust implementations across 5G core, transport, and access networks. Micro-segmentation, identity-aware access, and continuous verification.
Measurable Security Improvement
Results from a structured telecom SOC training program demonstrating detection capability improvement and blind spot identification.
MTTD Improvement
Mean Time to Detect improved by 62% after structured SOC training on telecom-specific threat scenarios.
ATT&CK Tactics
10 of 14 MITRE ATT&CK tactics now detectable by the SOC team, up from 6 at baseline assessment.
Blind Spots Found
Three critical detection blind spots identified and remediated through targeted Purple Team exercises.
Automated Reports
Monthly automated evidence reports generated for compliance audits and management review.
Built for India's Telecom Operators
Tailored training programs for every segment of India's telecom ecosystem.
BSNL
Post-breach remediation. Rebuild detection capabilities and train on the exact TTPs used in the 2024 breaches.
Jio
Zero Trust validation. Test and harden 5G core, edge, and subscriber data protection across the world's largest data network.
Airtel
AI-powered threat research. Advanced adversary emulation and threat hunting exercises for mature security teams.
Secure India's Telecom Networks
See how Critical Range builds network resilience for telecom operators with 5G-native, protocol-aware cyber training.