India's Most Advanced Indigenous Cyber Range
Built for the armed forces, paramilitary, and national security agencies. 100% sovereign. Zero foreign dependencies. Battle-tested at 42,000+ VM scale.
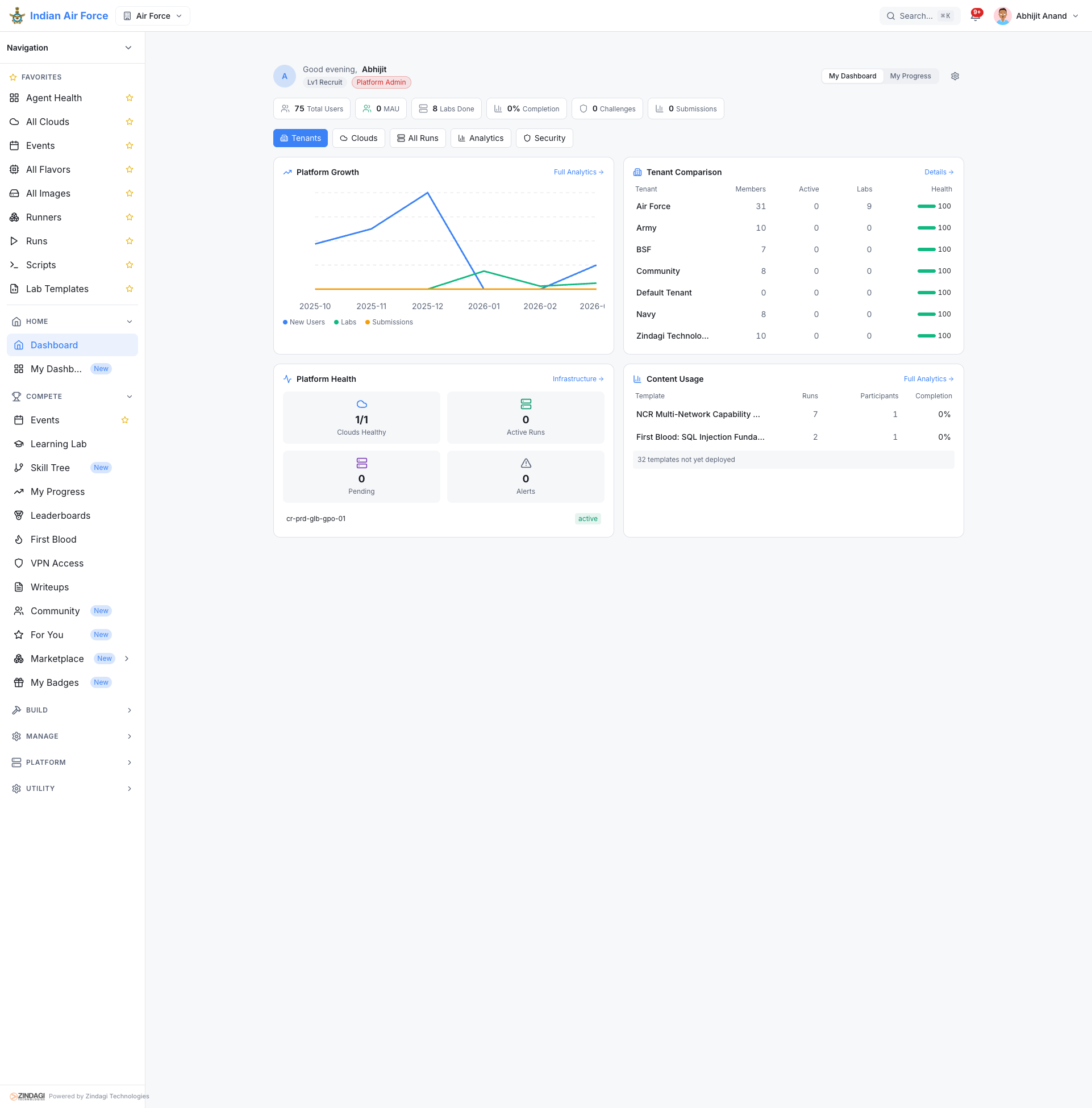
Production deployment showing Army, Navy, Air Force, and BSF tenants.
Four Levels of Military Cyber Training
From individual skill sharpening to national-level joint exercises, Critical Range covers the full spectrum of military cyber training doctrine.
Functional Training
Level 1Individual and small-team skill building across 850+ hands-on exercises. From SOC analyst triage to advanced malware analysis and digital forensics.
Planning & Coordination
Level 2Multi-team exercises with realistic command chains, inter-agency coordination, and joint operations rehearsal across cyber, signals, and EW domains.
Policy & Decision Exercise
Level 3Crisis simulation for senior leadership with AI-powered NPCs, branching scenarios, media pressure, and a Leadership Readiness Score.
Adversary Emulation
Level 4Full-spectrum Red Team operations with MITRE ATT&CK-mapped TTPs, APT campaign simulation, and real-time Blue Team response scoring.
Multi-Domain Superiority
Cyber alone is not enough. Critical Range integrates RF/EW, OT/ICS, and threat intelligence into a single unified training environment.
Cyber Operations
Network attack/defense, web exploitation, privilege escalation, lateral movement, and data exfiltration across enterprise and classified network topologies.
RF & Electronic Warfare
Spectrum monitoring, signal intelligence collection, jamming simulation, and radio frequency intrusion detection integrated into cyber exercises.
OT/ICS & SCADA
10 industrial protocols (Modbus, DNP3, OPC-UA, S7comm, BACnet, EtherNet/IP, PROFINET, IEC 61850, HART, CIP). 3 digital twin process models.
Threat Intelligence
OSINT collection, threat feed correlation, indicator enrichment, and attribution analysis woven into every exercise family.
Live Fire Exercise Support
NATO-style live-fire exercises with 20 concurrent team pairs. Red vs Blue on shared infrastructure with real-time scoring.
Wargames (ADX)
Simultaneous Red vs Blue team operations on shared infrastructure. Real-time flag capture, service uptime monitoring, and automated scoring.
Battle Stations (CDX)
Full-scale defensive operations against orchestrated attacks. Incident response, forensic analysis, and recovery under pressure.
Crisis Simulation
Executive decision-making with AI-powered stakeholder NPCs, cascading consequences, media pressure, and a Leadership Readiness Score.
Sovereign by Design
Every line of code written in India. Every deployment under your control. Full compliance with India's defence procurement framework.
DPM 2025 Aligned
Defence Procurement Manual 2025 category-compliant. Full indigenous IP. No foreign OEM dependency or technology transfer requirements.
Air-Gap Architecture
Zero telemetry, zero cloud sync, zero update beacons. Fully operational on isolated networks with no internet connectivity whatsoever.
Atmanirbhar Bharat
100% designed, developed, and maintained in India. Aligns with DAP 2026, IDDM classification, and Make-in-India defence procurement priorities.
On-Premises Sovereign
Deploy on your own hardware inside classified enclaves. Full source code audit available. No foreign jurisdiction exposure of any kind.
The Platform in Action
Real screenshots from defence exercise deployments.
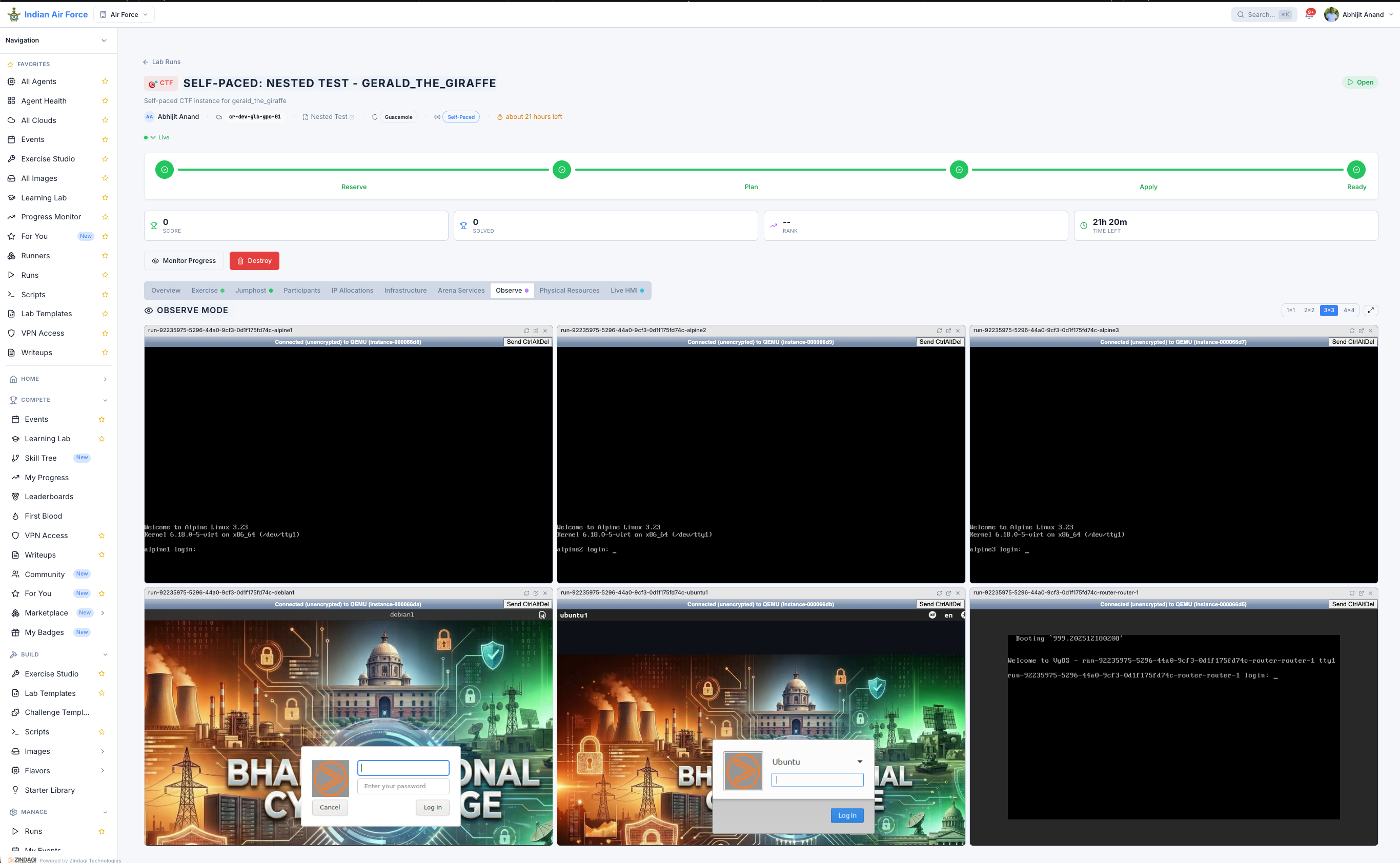
Real-time monitoring of participant VM sessions during live exercises.
Request a Classified Briefing
See how Critical Range powers national-level cyber exercises for India's defence forces. Secure briefing available for authorized personnel.