Cyber Investigation Training for India's Law Enforcement
From digital forensics to crisis command — the platform for MHA's Cyber Commando programme, state police cyber cells, and national investigation agencies.
The Cybercrime Challenge
India's law enforcement faces an exponential rise in cybercrime with a critical shortage of trained investigators. Closing this gap requires purpose-built training infrastructure.
Rising Cybercrime
500+/monthIndian states now handle 500+ cybercrime cases per month on average, a number that has doubled in the last three years. Most cyber cells lack the forensic training to investigate beyond basic phishing.
MHA Cyber Commando Programme
The Ministry of Home Affairs is building a force of 5,000 trained cyber commandos across state police, CAPFs, and central agencies. The programme demands a scalable, standardised training platform.
I4C Coordination Requirement
The Indian Cyber Crime Coordination Centre (I4C) mandates standardised investigation workflows across states. Training must align with I4C SOPs and NCRP reporting standards.
CCPWC/MOPF Funding Available
60:40 FundedCentral funding under CCPWC (Cyber Crime Prevention against Women & Children) and MOPF (Modernisation of Police Forces) is available at 60:40 centre-to-state split for cyber training infrastructure.
Six Investigation Training Tracks
Purpose-built training tracks covering every discipline a modern cyber investigator needs — from first-responder evidence handling to senior-officer crisis command.
Digital Forensics
Core TrackDisk imaging, memory acquisition, filesystem timeline analysis, and chain-of-custody documentation. Hands-on labs with real forensic images from simulated crime scenes.
OSINT & Cyber Intelligence
Social media intelligence, dark web monitoring, metadata extraction, and geolocation techniques. Build actionable intelligence from open sources without alerting targets.
Cryptocurrency & Financial Crime
Blockchain tracing, wallet clustering, mixer analysis, and exchange subpoena workflows. Train investigators to follow the money across Bitcoin, Ethereum, and USDT trails.
Malware Analysis
Static and dynamic analysis in isolated sandbox environments. PE header analysis, behavioral detonation, reverse engineering, and IOC extraction for court-admissible reporting.
Crisis Command
Leadership exercises for senior officers managing large-scale cyber incidents. Coordinate multi-agency response, media handling, and ministerial briefings under pressure.
Incident Response
First-responder triage, containment procedures, evidence preservation, and forensic handoff. Train officers to secure digital crime scenes before specialists arrive.
Built for Law Enforcement Training
Real product screenshots showing the tools investigators and trainers use every day.
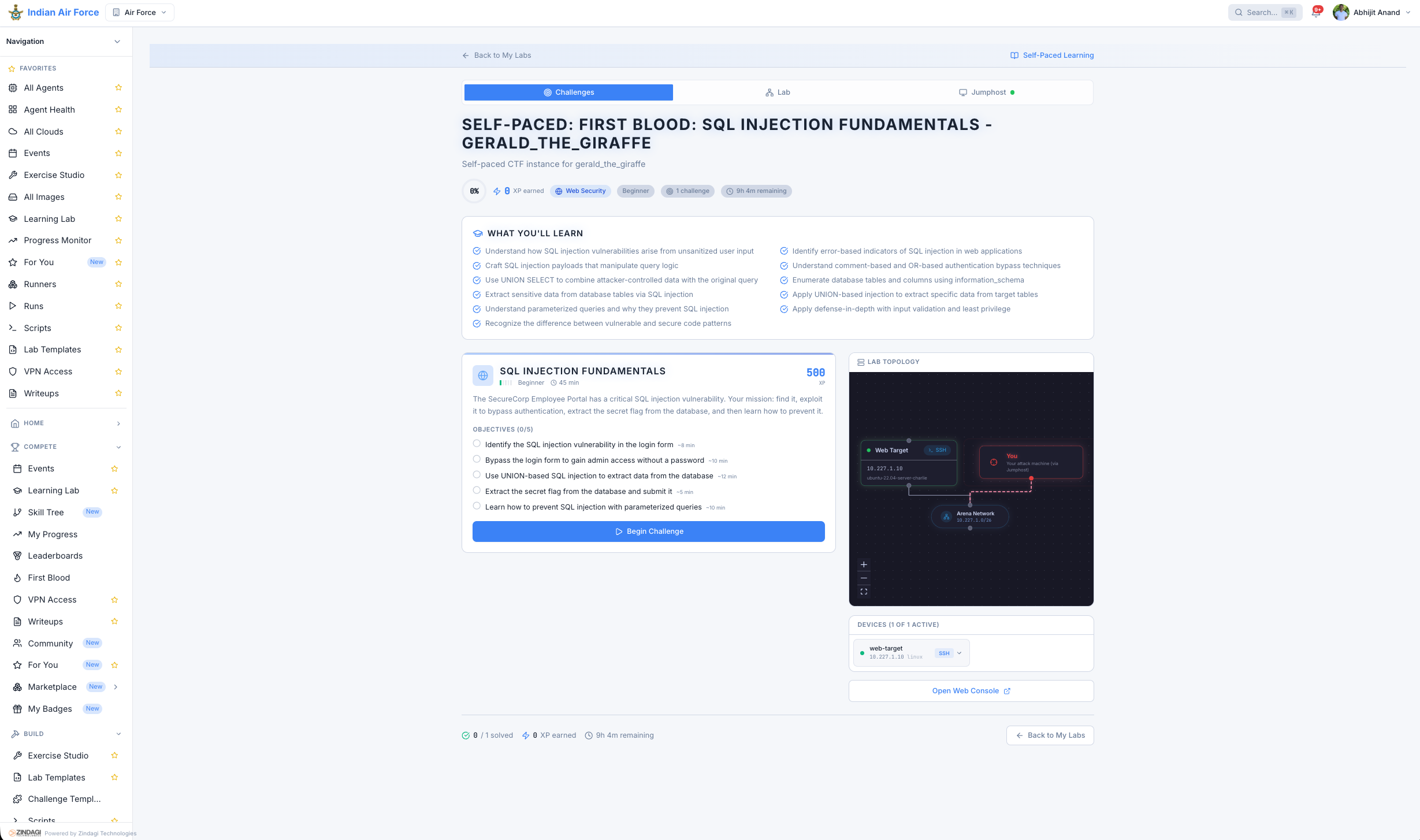
Step-by-step guided forensics labs with evidence chain tracking and auto-graded submissions.
State Police Cyber Cell Transformation
Investigator onboarding reduced from 6+ months to 2 months. Case clearance rate improved from 32% to 51%. 150+ investigators trained across 15 districts with standardised forensic methodology.
“For the first time, every district cyber cell follows the same forensic methodology.”
Funding & Procurement
Multiple central and state funding schemes cover cyber training infrastructure. GeM registration simplifies procurement for government buyers.
MHA CCPWC Funding
Central scheme under the Ministry of Home Affairs for cyber crime prevention. Covers training infrastructure, lab setup, and recurring platform licensing costs.
MOPF Scheme (60:40)
Modernisation of Police Forces scheme provides 60% central funding with 40% state share. Cyber training platforms qualify as modernisation infrastructure.
State Police Modernisation Fund
State-level police modernisation budgets can be directed toward cyber investigation capability building. Multiple states have earmarked funds for cyber cell upgrades.
GeM Registration
GeM ListedCritical Range is registered on the Government e-Marketplace (GeM) for simplified, compliant procurement. Direct purchase or L1 bidding — no lengthy tender cycles.
Build Your Cyber Investigation Capability
See how Critical Range trains the investigators who protect India's digital citizens.